Last year, the Canadian government pushed Bill C-2, which would erode Canadian digital rights in the name of “border security.” The bill was so bad it didn’t even make it to committee because of the backlash from the privacy community. Now, the spring’s worst sequel, Bill C-22, aka The Lawful Access Act, is trying it again.
As with most sequels, Bill C-22 makes some tweaks to problematic elements, but largely retains the same problems. The bill forces digital services, which could include telecoms, messaging apps, and more, to record and retain metadata for a full year, and expands information sharing with foreign governments, including the United States. Metadata can reveal a lot about who you communicate with, where you go, and when you do so. Expanding the collection of metadata would require companies to store even more information about their users than they already do, providing an incentive for bad actors to access that information.
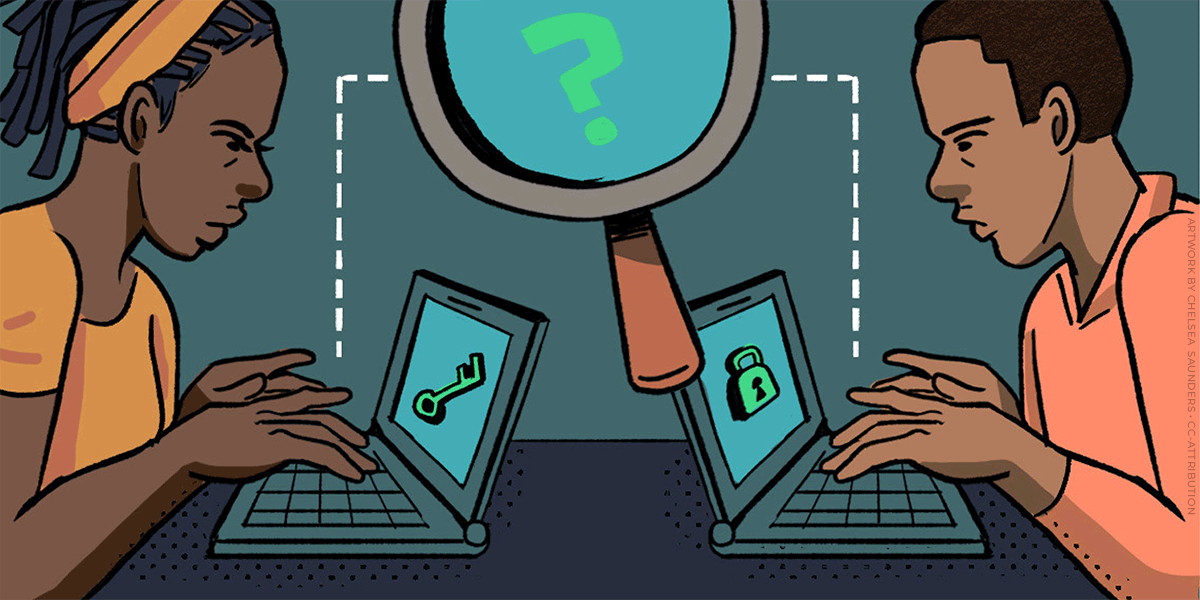
Worst of all, Bill C-22 erodes the privacy of millions by providing a mechanism for the Minister of Public Safety to demand companies create a backdoor to their services to provide law enforcement access to data, as long as these mandates don’t introduce a “systemic vulnerability.” These widespread surveillance backdoors would likely facilitate even more data breaches than we see already. The bill also bans companies from even revealing the existence of these orders publicly.
The definitions of both “systemic vulnerabilities” and “encryption” are not clear enough in C-22, leaving wiggle room for the government to demand that companies circumvent encryption. And the overbroad definitions in the bill can include apps as well as operating systems. Canadian officials have made it clear they believe it’s possible to add surveillance without introducing systemic vulnerabilities, which is just not true. Surveillance of encrypted communications is fundamentally a systemic vulnerability.
This resembles what happened in the UK last year, when the government demanded that Apple implement this type of backdoor into its optional Advanced Data Protection feature, which then forced Apple to revoke the feature for its UK users instead of complying with the request. To this day, UK users still do not have access to this powerful, privacy-protective feature that provides stronger protections for data stored in iCloud. Both Meta and Apple are concerned that C-22 would give the Canadian governments similar powers, and both companies have come out against the bill. The U.S. House Judiciary and Foreign Affairs committees also sent a joint letter to Canada’s Minister of Public Safety highlighting the concern around backdoors into encrypted systems.
The dangers of these sorts of backdoors are not theoretical. In 2024, the Salt Typhoon hack took advantage of a system built by Internet Service Providers to give law enforcement access to user data. When you build these systems, hackers will come.
Canadians deserve strong privacy protections, transparency into how companies handle user data, and clear safeguards around encrypted data. Bill C-22 provides none of that, instead reaching further into the digital pockets of tech companies to build broad lawful access mechanisms.
Further reading